Raysync Security Design: Account&Password Protection
December 11, 2020
Raysync is designed with multiple security protection based on the account number and password of the user. Specific security design is as follows:
Account protection security design
Login authentication has a built-in anti-violence cracking mechanism, if the user enters the wrong password five times within 3 minutes, the account will be automatically locked.
Session identification in login is generated by using the interface of OpenSSL high-strength random function RAND_bytes () to prevent random information from being hit by the simulator.
Password protection security design
In the transfer process, the user password is encrypted by the asymmetric high-strength encryption algorithm, and even if the transfer message is intercepted, the attacker can not recover the plaintext through ciphertext.
The information stored in the database of the user password is irreversibly encrypted 10,000 times in one direction by using the PBKDF2 algorithm and the user's individual random salt. Even if the database information is leaked, the user password cannot be reversed through ciphertext.
The password must be a combination of case, number and special symbols, and the length is greater than or equal to 8 characters.
The system provides a weak password dictionary. Users can customize weak passwords that meet the password strength but are easy to be cracked by social engineering. System users are prohibited from using such passwords, such as < company English name > @123.
As a one-stop solution provider, Raysync has independently developed its core transfer technology with its professional technical teams to offer high-performance, secure, and reliable large file transfer and file management services for major enterprises.
You might also like
User Guide
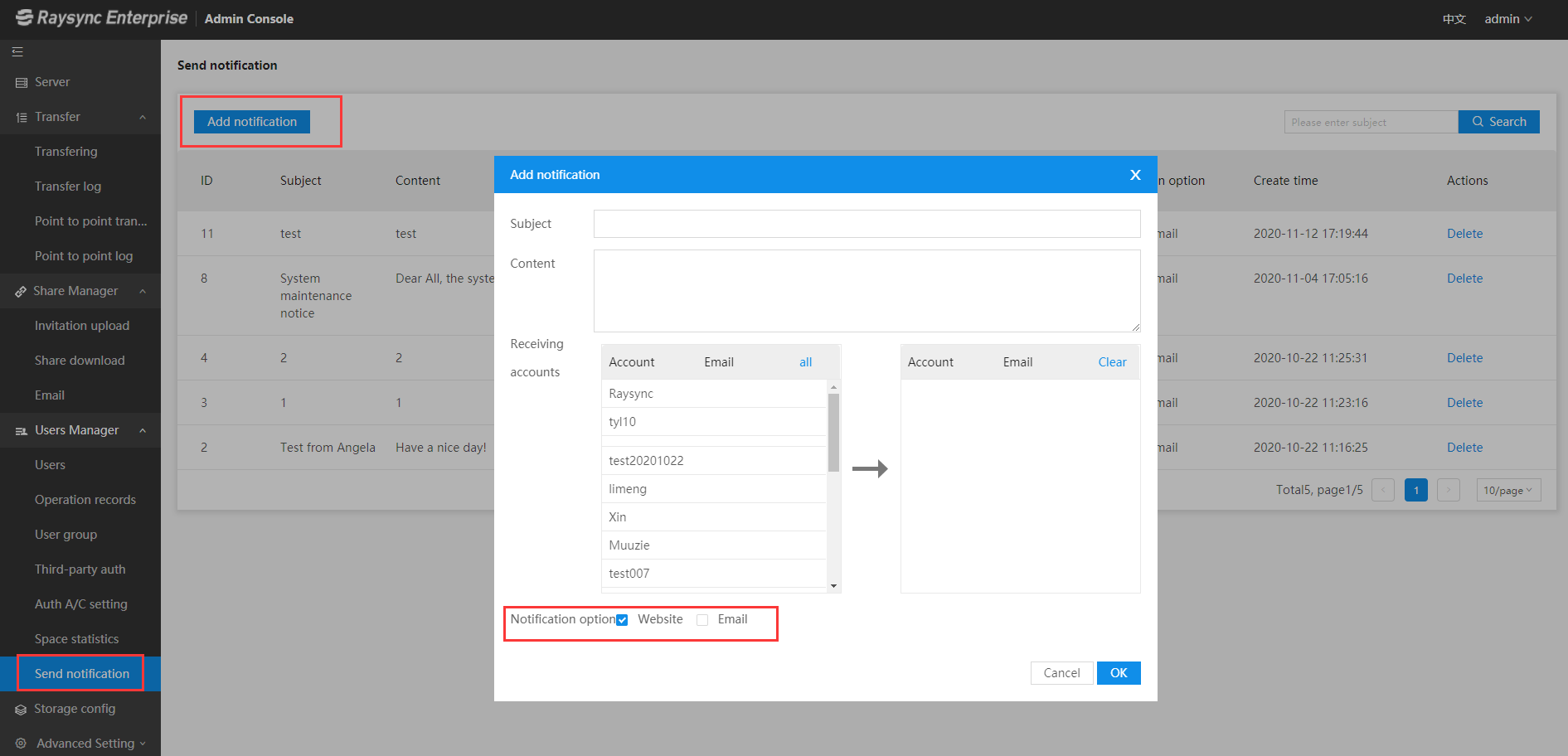
November 12, 2020Note: Sender mailbox, mailbox display logo, and company name are configured by the administrator in the admin console.

User Guide
December 26, 2023The one-stop solution adopts the completely self-developed RadiumSpeed high-speed transmission technology, which greatly improves the efficiency of film and television production and distribution.

User Guide
July 8, 2021Today, companies in all walks of life are facing greater challenges in quickly and reliably moving large files and massive data sets between global sites and teams.