Filter News
Raysync News
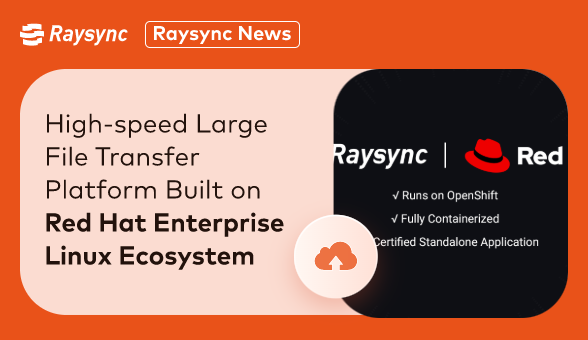
September 11, 2023Raysync, a leading provider of high-performance file transfer solutions, has announced a strategic partnership with Red Hat, the world-renowned open-source software and solutions provider.

This article briefly introduces how to send large videos and what are the methods of transmission. If you want to learn more, you can click here!

File synchronization is the process of ensuring that two or more locations contain the same latest files. If you add, change or delete files from one location, they will sync to another location.

The Mammoth International Contest on Omics Sciences (MICOS) is a global contest in biology science, held from June 8 to November 4. Raysync is the co-organizer of this contest.

How big is a movie file? This article talks about the size of a movie file, and why, including if transferring a large movie file. Click to learn more!

Case Studies
October 18, 2022Raysync has a successful collaboration with Rusk Media, this time Raysync interviewed Mr Udhay, the head of the post-production from Rusk Media, click to learn more!
![[2022] The Fastest File Transfer Method Between PC and Mobile Device](http://images.ctfassets.net/bg6mjhdcqk2h/4TrdHhddMhChhtynZdsvhU/6dcd2ff1d424fbc723a67e466482be25/transfer-files.jpg)
The transfer of files from PC to mobile is easy. This article introduces the five fastest ways to transfer files from a mobile device to a computer.

Raysync News
September 28, 2022The amount of data transferred between global business networks is very large. Through this article you can know everything about big data. Click here to learn more!
![[2022] The Best Secure File Transfer Solution](http://images.ctfassets.net/bg6mjhdcqk2h/46AYlbzL5fGw0HkHAPBF36/f66263849287a312759c14e367826e48/the-best-secure-file-transfer-solution.jpg)
The security of enterprise digital assets is facing increasingly severe challenges. How to ensure that enterprises are not intentionally or unintentionally leaked during file transfer has become an urgent problem for enterprises.

Raysync News
September 22, 2022Explore differences between synchronous and asynchronous data transfer, their roles in computer architecture, and modern solutions like Raysync.