Filter News
User Guide
User Guide
December 11, 2020The system provides a weak password dictionary. Users can customize weak passwords that meet the password strength but are easy to be cracked by social engineering.

User Guide
December 9, 2020HTTPS TLS 1.1, TLS 1.2, TLS 1.3, only open the encryption algorithm suite recognized by the industry as safe;
User Guide
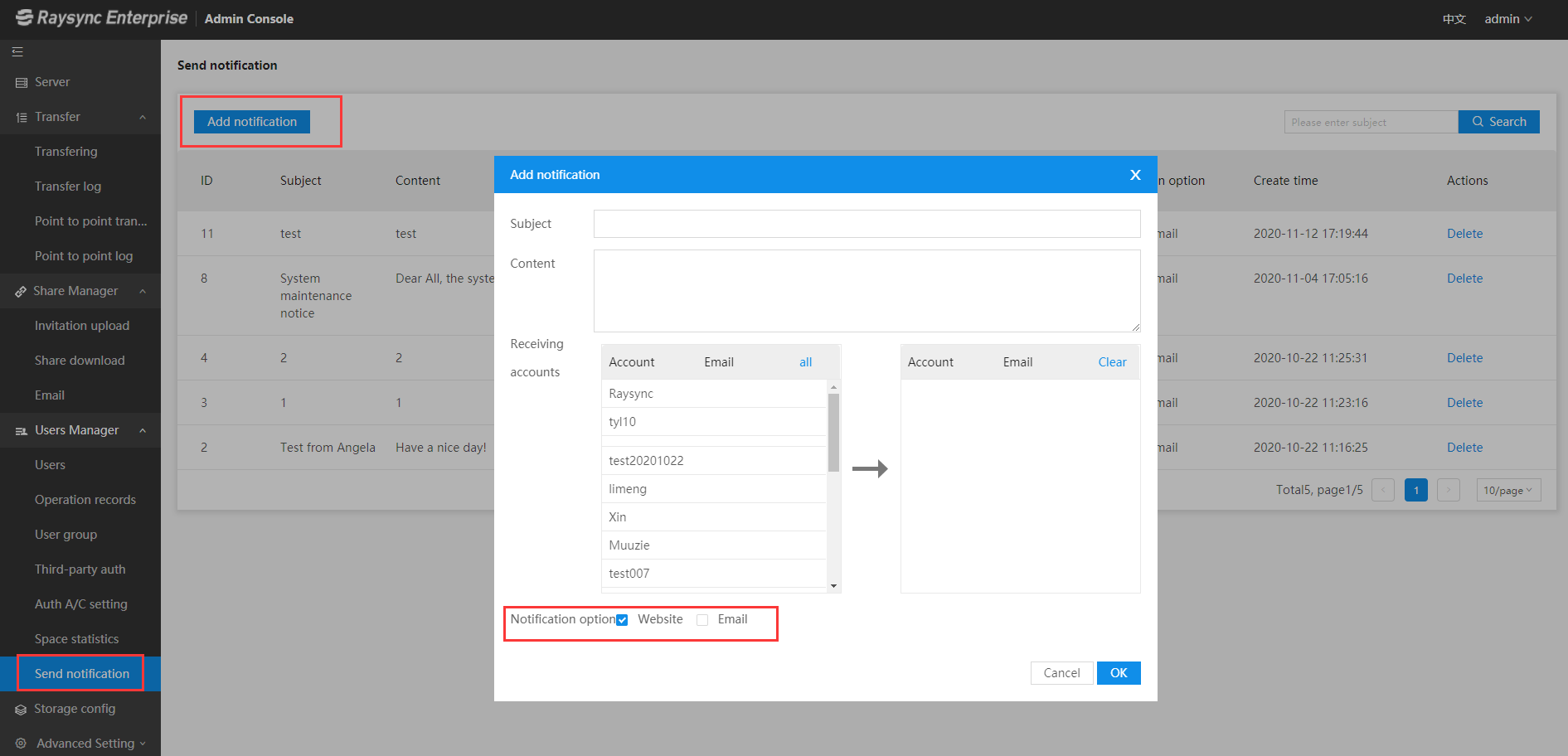
November 12, 2020Note: Sender mailbox, mailbox display logo, and company name are configured by the administrator in the admin console.